In Cybersecurity
Top 5 Cybersecurity Trends 2021 and Beyond - read the full article about Cybersecurity 2021, Cybersecurity and Network security and pen testing from Cybersecurity Leadership on Qualified.One

Youtube Blogger

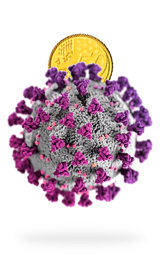
When you are a cybercriminal, you crave chaos.
The coronavirus pandemic has been a boon for cybercriminals looking to make money amid uncertainty and fear.
The global pandemic has led to an epic rise in people working from home, shopping online, and generally being more digitally connected than ever before.
If you work from home, I know how your schedule looks like.
Anyhow, the cyber incident numbers are staggering and scary.
The FBI recently reported that the number of complaints about cyberattacks to their Cyber Division are up 400% or as many as 4000 a day.
Tanium, a security vendor, surveyed global CXOs and they found out that 90 percent of the organizations experienced an Increase in Cyberattacks due to COVID-19.
So, what are we talking about here? Cybercriminals spun up coronavirus-centric phishing attacks, spoofing the WHO, the government, and even the COVID tracker sites.
Scumbags.
Some of them deployed fake VPNs and harvest data from nefarious VPN providers.
It is the primary reason why the Cybersecurity stocks such as CrowdStrike, Zscaler, FireEye, and Palo Alto Networks posted substantial gains in 2020.
Last year, AWS and Google suffered massive DDoS attacks, we’re talking about getting slammed with traffic over 2 terra bits per second, then SolarWinds hack happened and now the Microsoft Exchange server hack.
The remote work has sent enterprises scrambling to protect their cloud infrastructure from endpoint-based attacks.
So, in this video, I want to discuss how the pandemic and the new normal are going to reshape the cybersecurity landscape for years to come.
Let’s get started.
Oh wait, don’t forget to gently click that Like button, don’t smash it.
Be right back.
Hi.
My name is Afaq.
Hope you’re doing good.
So, why didn’t the shopper go down the canned meat aisle in the grocery store? And the answer is Her SPAM filters were on.
OK, so the Gartner says that the cybersecurity spending is expected to reach $123 billion, whereas the global cybersecurity losses are going to tally up to a Trillion dollars in 2020.
It is expected that by 2025, the cybersecurity losses will surpass 10 trillion dollars annually or twice the size of the entire IT spending worldwide in that year.
Let that sink in for a second.
These are mind-boggling statistics and a lot of zeros to wrap your head around.
According to PwC’s 2021 Global Digital Trust Insights report, 55% of the enterprise executives said their cybersecurity budgets will increase this year.
According to Gartner, by 2025, 40% of boards of directors will have a dedicated cybersecurity committee overseen by a qualified board member, from less than 10% today.
Gartner also believes that regulatory compliance and cybersecurity are two of the biggest sources of risk for the enterprise today.
It is estimated that the cybersecurity industry will have over 3.5 million vacant positions this year.
So, if you are a new grad or someone switching IT careers, this might be best time to consider a career in cybersecurity.
Now, looking into my crystal ball, I can see five trends dominating the cybersecurity landscape for years to come as a result of the coronavirus pandemic.
Number one and you guessed it right, the SolarWinds attack has shown us that there is a virtually unlimited attack surface that exists within the software supply chain.
A security expert, Alex Birsan, was able to hack into Apple, Microsoft, Tesla, Netflix, PayPal by injecting a malware into public repositories which often contain dependencies for software projects.
When you use a package installer, like npm for Node.js and pip for Python, and every time you download and use a package from any of these sources, you are essentially trusting its publisher to not have a backdoor inside those dependencies.
So, can this blind trust be exploited by malicious actors? Absolutely.
None of the package hosting services can ever guarantee that all the code its users upload is malware-free.
According to Alex, past research has shown that typosquatting like when an attack leverages typo’d versions of popular package names, can be incredibly effective in gaining access to random computers around the world.
Many companies use both private and public dependencies in their source code.
Public dependencies can be uploaded to open-source repos such as GitHub by virtually anyone, meaning that they could carry malicious code.
IQT Labs, now maintains a living document, though not breathing, on the GitHub that contains a list of all known supply-chain compromises that have taken place to date.
When researching for this video, I found about 154 entries in there.
What’s worse, even the cybersecurity vendors are not beyond the reach of supply chain attackers.
In the case of SolarWinds hack alone, FireEye, Malwarebytes, Mimecast, and Microsoft were breached.
Now, the difference is that these vendors have the bench strength to conduct a thorough investigation, like Malwarebytes went through their entire build and delivery processes including reverse-engineering their own code looking to find any possible backdoors added by the SolarWinds hackers.
While supply chain attacks have recently picked up the pace, they are not new.
If you remember, back in 2011, RSA Security confirmed that their SecurID tokens were hacked and one of its customers, Lockheed Martin, was attacked as a result.
What’s more? The commercial software isn’t the only target, since over 90% of all applications contain open-source code, that makes open-source a good target.
Attackers do not have to wait around for a vulnerability to surface in open-source software, they are now actively compromising the open-source development or distribution process.
Here is the meta question.
So, how do we guard against the supply chain hacks? There are plenty of general frameworks such as those in the financial or healthcare sectors, that call out for the third-party software risk assessment.
For Federal agencies, there is FIPS-140 accreditation, I know from my first-hand experience that it is a pretty expensive certification process and one that’s limited to K9 software.
There are also general frameworks such as Capability Maturity Model or CMM, ISO 9001, Common Criteria, and SOC2.
I don’t think we can wait for a magical supply chain security framework to appear one day, what enterprises need to start doing is to ask the right questions during the Request For Proposal or RFP process and push the vendors to answer them.
For example, what kind of security posture do they have? what kind of code verification mechanisms do they have in place? You get the idea.
There is one standard waiting in the wings that looks promising to me and that is Consortium for Information and Software Quality.
One of the standards the organization is working on is known as the SBOM.
Like a bill of materials or BOM for physical items, the SBOM is a comprehensive inventory of the software raw materials, the subassemblies, parts and components, needed to create a software product.
As I said, this is in the works, and the group plans to submit the specs for approval to the Object Management Group, their parent organization, by June this year.
For what it’s worth, Microsoft, the Linux Foundation, and the other big players are involved in that working group.
Link is in the description, so be sure to check it out if not already.
Another approach that I have proposed before is to have a whitelist for every workload that needs to communicate with another workload especially something outside on the Internet.
Every vendor should provide that whitelist in the form of a manifest as part of their software package.
If there is an attempt to access something outside that whitelist, the infosec staff should be alerted.
Enough said.
Now, going back to my crystal ball, the second on my list is the Internet of Things or IOT breaches.
The security industry has put an enormous amount of focus on protecting the endpoints and user-to-machine traffic and while not perfect I believe we’re in great shape there.
How do I know? Did you ever question why hackers have ventured into the supply chain attacks? In my opinion, the cybercriminals are always looking for the path of least resistance so why make so much effort to compromise an endpoint inside an enterprise when you can just compromise a partner and land inside not just one but thousands of them.
Supply chain attacks were always possible, but no one bothered in the past, why do so when you could simply hack a firewall or own an endpoint inside an Enterprise.
Anyhow, recently Verkada, a quote, and quote enterprise-grade surveillance camera startup, out of Silicon Valley, was hacked and as a result, a who’s who list of enterprises were exposed.
Among other things, hackers were able to peek into the Tesla factory in Shanghai, showing workers on an assembly line.
According to the activist hackers, they accessed 222 cameras displaying activity inside Tesla factories and warehouses.
Tesla says the hack was restricted to a supplier’s production site in China, but its Shanghai car factory and showrooms were not affected.
Anyhow, here is what happened.
The hackers gained access to Verkada through a Super Admin account.
This gave them access to the cameras of all of the company’s customers.
This was likely done through a phishing attack that was made more convincing perhaps via some social engineering on steroids.
Speaking of IOT best practices, every enterprise that uses IoT devices must place them on an isolated LAN segment and IP subnet, so even if they are compromised, they can’t be used as a botnet and avoid another Mirai botnet fiasco.
In the case of Verkada, once you get access to super admin or root and the attack is underway, there is nothing you can do downstream as an enterprise to stop the breach other than turning off your cameras or cutting the camera access to the Verkada cloud.
All machine-to-machine communication must be secured with special-purpose accounts and again a whitelist approach should be applied so that only the intended communication can take place.
So, what else? Work from Home.
Remote work and virtual meetings are here to stay.
So, if you are a CISO, take your zero trusts seriously by putting it on the top of your list for 2021.
Without zero trust, you are putting your company and your career at risk.
It is estimated that more than 75% of the businesses still have four or more on-premise applications that remote workers need to access, which means VPNs are here to stay.
There are plenty of vendors out there that provide zero trust solutions such as Cisco, Palo Alto, Illumio, Zscaler, and others.
Number four.
Move your applications to the cloud.
Just about with every breach, we’re reminded that enterprises should consider moving their applications out of their data centers and into the cloud.
The evil big tech can reliably run your workloads and they have the Infosec and DevOps teams to keep them running securely while meeting your SLAs.
Now, I want to make one thing clear.
It is not that software hosted in the cloud, as opposed to being on-premise, magically becomes secure.
It does not.
What makes the cloud software secure is the operational excellence and the software chops, the likes of AWS and Google possess.
I understand that not every workload is suitable for the cloud, but if you were running your network performance monitoring in the cloud, you were not breached when your NPM vendor SolarWinds was compromised and the same can be said for Microsoft Exchange versus Microsoft Exchange Online or Office 365.
Number five and finally, recognize that the cyber pandemic is here to stay, and we can’t vaccinate our way out of it.
So, now is the time to pull out all the stops and take action to protect your organization.
Remember, remote workers will be targeted by cybercriminals.
If your IT spending budget got cut, a trend that is likely to continue in 2021, then you can save some by turning to platforms like secure access service edge or SASE to consolidate your security management.
THANK you for watching the video, I hope you found it helpful.
I’d love to hear your thoughts and I will see you back here on Monday and Friday sometimes on Wednesday.
I will see you soon.
Bye for now.
Cybersecurity Leadership: Top 5 Cybersecurity Trends 2021 and Beyond - Cybersecurity