In Cybersecurity
Why The U.S. Cant Stop Cyber Attacks - read the full article about Cybersecurity 2021, Cybersecurity and Network security and pen testing from CNBC on Qualified.One

Youtube Blogger

Unknown: This is probably the most significant ransomware attack on one of our critical infrastructures ever.
Colonial Pipeline is the operative largest pipeline Last month, hackers took our gasoline hostage now theyre carrying fuel from the Gulf Coast to the northeast, it was hit with a ransomware attack.
attacking our meat supply.
JBS says units in Australia and North America were hit over the weekend by what the company is calling an organized cyber attack on its information system.
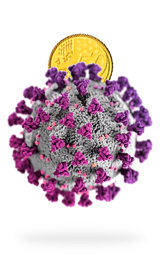
The US recently faced a series of ransomware attacks and they arent showing signs of slowing down anytime soon.
Although ransomware has really been around since 2013, it is not yet been seriously taken in terms of something that could impact critical infrastructures such as the Pipeline.
Ransomeware, a program that hackers use to hold digital information hostage, has become the top choice of malware for criminals. Mark Bleicher negotiates these hostage situations for victims.
We have a 911 line similar to how you would have a 911 for the police if you need to call. So well get an email from a client or an insurance carrier or a law firm saying that they have someone who was just hit with ransomware, and the next steps is for us to assemble and get on a call.
And lots of money is at stake. In 2020, the total amount of ransome paid by the victims reached nearly 350 million dollars worth of cryptocurrency. A 311% increase compared to the previous year. Plus it takes a serious emotional toll on the victims.
Violated they have gotten into our network and into places that we dont know where theyve gotten. We dont know what systems they have touched. It is definitely a moment of realization that the things you thought you were protected from the layers that you had in place they wrote around them, they customize their attack and wrote systems to infiltrate and destroy.
So what led to the rise of ransomware in the US and what makes it so difficult to fight them. What makes ransomware so effective is its capability to entirely disrupt an enterprise or infrastructure like the Colonial Pipeline, it usually makes its way in via a phishing email or network connection that isnt secured encrypting the victims file to prevent access.
The malicious actor then demands a ransom in exchange for decrypting the files held hostage Highest Ive ever seen was about 70 million.
This is Mark Bleicher, and he has a job like no other as the managing director at Arete Incident Response. He is on the front line in a battle against ransomware. In the United States.
In the beginning of 2020, we start to see a new trend that is The negotiation then takes place in a chat room on the dark web now prevalent throughout the industry where not only did they encrypt your data, but they also had stole that data and then they threatened to post or leak that data if the ransom isnt paid. So that really has driven up the ransom demand because from the victims perspective, you have to consider Well, we need to pay to get our data unlocked, or we pay to have that not leaked.
that can be located via a unique identifier included in a digital ransom note. Thats where Bleicher speaks with the bad actors on behalf of the victims.
These sites have a chat feature much like youd see on any retail site if you had a question about a product. And thats how you get the conversation going is you start a conversation within the chat thats on their site.
If the victim makes up their mind to pay the ransom, and the amount is negotiated, the payment is made via cryptocurrency. Bitcoin is the most popular choice, accounting for 98% of ransomware payments in the first quarter of 2019.
That may change now that the US officials were able to seize $2.3 million in Bitcoin paid to hacker group Darkside following the Colonial Pipeline attack.
Once the payments have been made, the criminals send a decryption key. And the cycle goes on to repeat itself with another vulnerable business or infrastructure.
I can tell you over the last two years, and its well into the millions, hundreds of millions victims that weve come across.
Ransomware has grown into a multi billion dollar industry.
And surprisingly, a majority of the ransom paid is shared amongst a relatively small number of criminals. A recent study found that 199 deposit addresses received 80% of all the funds in 2020 and an even smaller group of 25 addresses accounted for nearly half. The hacking syndicate behind these attacks are often highly organized with self given names like Evil Corp or Darkside.
We have to all realize that the cyber crime ecosystem is a business. It is a large underground business. It has all elements similar to a legitimate legal business. And so there are partnerships and there is malware developers and there are distributors.
First and foremost, you know, Im a security practitioner, most of us never thought that we would get into a situation where we would be negotiating for essentially the life of a company.
These groups have become increasingly bold, showing off bundles of cash and fancy sports cars. Thats because tracking, arresting and bringing these hackers to justice is incredibly difficult.
Its notoriously difficult to attribute cyber attacks. Its an ongoing challenge for governments. And so from an organizations perspective, whether its a criminal group, or whether its a nation backed group, it often has little A lot of these organizations are allowed to essentially operate consequence.
freely within Russia or other former Soviet states, as long as they dont hit anybody within that country or former Soviet state. So unless theres a cooperation at the political level there, I dont see this going away anytime soon. Look how much money has been shelled out over the last five years, let alone the last two, its mind blowing. So its a booming industry.
Ransomware attacks impact almost every sector of the American economy.
Unfortunately, its become a bit of the sort of classic modus operandi for many hackers and criminals. And what youre seeing also is that its pretty indiscriminate in terms of the industry sectors that it targets.
In 2020. Professional and public service and manufacturing were the three industries that were hit the hardest, followed closely by healthcare, technology and finance. In 2020, a ransomware attack may have also claimed its first life after taking a hospital offline in Germany.
It has a real cost. There was a study done by Barrons early in January that said that the estimated cost of ransomware in 2019, was about 11 point 5 billion in 2020. It is 20 billion. It didnt exactly double but it got close enough to doubling. So theres a real financial cost to businesses around ransomware.
Ransomware has also grown sophisticated enough to target government entities and critical infrastructure in recent years, resulting in costly shutdowns.
Its disturbing that there are people out there that would take down systems for you know, things like health care, things like government, we provide water for our city as well as many other cities, they have no concern or care for their fellow human, its disturbing.
In May of 2021, the city of Tulsa experienced several technical difficulties following a ransomware attack.
You may try to open up Microsoft Word, for example, and it wont open part of its system was actually encrypted. Or you may try to open up a document that you created, that document is encrypted, and so it cant read it.
Besides the inconvenience, being a victim of ransomware can be a harrowing experience.
Theres a range of emotions, you know, some clients are extremely angry. One of the questions is why cant they know our government go after these organizations, a lot of these victims are also in shock, you know, how could this happen to us.
Violated they have gotten into our network and into places that we dont know where theyve gotten, we dont know what systems they have touched. It is definitely a moment of realization that the things you thought you were protected from the layers that you had in place that they wrote around them, they customize their attack, and wrote systems to infiltrate and destroy.
In order to stop the money flowing into the industry. The US government has historically discouraged individuals and businesses from paying their hackers. In fact, according to the Department of Treasury, paying the ransom to criminals is illegal if the hackers demanding the ransom, were subject to US sanctions. But this leaves many businesses in a tricky situation.
If youre an organization thats been struck by ransomware, its a tough situation to be in. Its not ideal to be paying these ransoms. These are criminal organizations. And of course, there is a whole effort, law enforcement at government level to stave that activity and clearly paying ransom fuels the industry.
And even if the business chooses not to pay the ransom, there is the cost of recovery to consider the average cost of recovery from ransomware attacks ballooned to 1.8 5 million in 2021, more than doubling from the previous year. That makes the average cost of recovery 10 times bigger than the size of the actual ransom payments.
We dont know the total cost at this point, because were in the middle of recovery. would it cost more than the ransom? Quite potentially, yes.
The shutdowns are incredibly costly. Theyre labor intensive.
They require experts of which often we dont have enough.
The challenge for us is that they encrypted partial systems.
And so basically, we have to go through and check every single system and verify that A its not damaged B its not got something on it from the actual attacker and then see that it can still be used for production. Its a long and arduous process to do that damage assessment. And the larger your network is, the larger your application base is, the more disruptive it can be.
The 2021 Colonial Pipeline incident sent shockwaves across the oil industry and the US government, alerting them on the severity of cybersecurity concerns. Shortly after President Biden signed an executive order to strengthen US cybersecurity defenses. When nearly half of the congressional districts across America hit by some sort of ransomware attack from 2013 to 2020, voices in support for more regulations are growing.
These are criminals that hit us in our communities, they lock up our schools our hospitals our government agencies, and we need to put an end to it. There are a number of things I think the administration can do. But its going to take a collective defense effort, its going to take industry, government, and international partnerships.
Federal law doesnt directly address ransomware attacks, its instead covered under a broad umbrella of cybercrime laws like the Electronic Communications Privacy Act and the Computer Fraud and Abuse Act. Congress has instead focused more on providing state and local governments with enough resources to fight against cyber attacks. In 2018, President Trump established the Cybersecurity and Infrastructure Security Agency or CISA, to improve cybersecurity across all levels of government. Meanwhile, house lawmakers rolled out a bill to invest 500 million in state and local cybersecurity in May 2021.
At both the state and local government, I dont think we have enough guidance on this from a legal perspective. And yeah, I dont think its clear enough. I think the law needs to address these situations where companies are forced to either go out of business or they pay the ransom, what are we doing for companies that are in that position? additionally, how are we incenting companies to do the right thing and be prepared relative to ransomware.
Some states like Michigan, California and Wyoming have taken matters into their own hands passing laws that make it illegal to even possess any sort of ransomware. But theres still a lot of work that needs to be done, especially when it comes to critical infrastructure. Roughly 85% of Americas critical infrastructure is privately owned, and private sectors arent required to follow the strict cybersecurity guidelines set by the government.
From a critical infrastructure standpoint, theres an awful lot we need to do to make this a better security system. But weve got electrical grids in this country, we have water systems, we have pipelines, we have a lot of critical infrastructure that is really open to some of these ransomware attacks and cyber attacks. An we need to do a much However, the US might prepare against future threats. One thing is for certain, the recent series of attacks on American businesses and the government isnt the end. But the start of many future ransomware attacks to come.
We have to be prepared that it will happen again, weve dealt with smaller incidents of ransomware where a single persons files were affected and we just restored from backup moved on. But I think the reality is right now, its something we have to be prepared for. At any time, the amount of impact its going to continue to have will grow and I think the amount of money to be made will continue to grow. I dont know where that will peak out. And I dont know if its just gonna morph into something even more dangerous and scary.
Its hard to say. But I dont think were at the peak yet.
CNBC: Why The U.S. Cant Stop Cyber Attacks - Cybersecurity